The current threat landscape is rapidly advancing, with cybercriminals constantly upgrading their toolset to break through security defenses. If you want to outsmart malicious hackers, it’s time to start thinking like them. Fend them off with various layered defense methods. This is what Defense in Depth (DiD) is all about.
The National Institute of Standards and Technology (NIST) defines DiD as “The application of multiple countermeasures in a layered or stepwise manner to achieve security objectives. The methodology involves layering heterogeneous security technologies in the common attack vectors to ensure that attacks missed by one technology are caught by another.”
In simple terms, DiD is a cybersecurity approach in which multiple defensive methods are layered to protect a business. Since no individual security measure can guarantee protection against every attack, combining several layers of security can be more effective.
If you want to protect your business against cybercriminal masterminds, stay up to date with the ever-changing threat landscape.
9 Threats to Protect Your Business Against
While there are numerous threats that businesses like yours must be aware of, let’s take a look at some of the most common.
1. Ransomware
Ransomware is a type of malware that threatens to disclose sensitive data or blocks access to files/systems, by encrypting it, until the victim pays a ransom. Failure to pay on time can lead to data leaks or permanent data loss.
2. Phishing/Business Email Compromise (BEC)
Phishing is a cybercrime that involves a hacker masquerading as a genuine person/organization primarily through emails or sometimes other channels like SMS. Malicious actors use phishing to deliver links or attachments that execute actions such as extraction of login credentials or installation of malware.
Business email compromise (BEC) is a scam that involves cybercriminals using compromised or impersonated email accounts to manipulate victims into transferring money or sharing sensitive information.
3. Cloud Jacking
Cloud jacking, or cloud hijacking, entails the exploitation of cloud vulnerabilities to steal an account holder’s information and gain server access. With an increasing number of companies adopting cloud solutions since the pandemic hit, IT leaders are worried about cloud jacking becoming a significant concern for years to come.
4. Insider Threats
An insider threat originates from within a business. It may happen because of current or former employee(s), vendors, or other business partners who have access to sensitive business data. Because it originates from inside and may or may not be premeditated, an insider threat is hard to detect.
5. Denial-of-Service/Distributed Denial-of-Service (DoS and DDoS)
These attacks are common and easy to carry out. When DoS or DDoS attacks happen, hackers flood the targeted system with multiple data requests, causing it to slow down or crash.
6. Artificial Intelligence (AI) and Machine Learning (ML) Hacks
Artificial intelligence (AI) and machine learning (ML) are two trending topics within the IT world for their path-breaking applications. However, AI and ML help hackers be more efficient in developing an in-depth understanding of how businesses guard against cyberattacks.
7. Internet of Things (IoT) Risks and Targeted Attacks
IoT adoption is skyrocketing, and experts estimate that the total number of installed IoT-connected devices worldwide will amount to 30.9 billion units by 2025.1 However, data sharing with no human intervention and inadequate legislation has made IoT a favorite target of cybercriminals.
9. Web Application Attacks
Vulnerabilities within web applications permit hackers to gain direct access to databases to manipulate sensitive data. Business databases are regular targets because they contain sensitive data, including Personally Identifiable Information (PII) and banking details.
9. Deepfakes
A deepfake is a cyberthreat that uses artificial intelligence to manipulate or generate audio/video content that can deceive end users into believing something untrue.
Get Up and Running With DiD
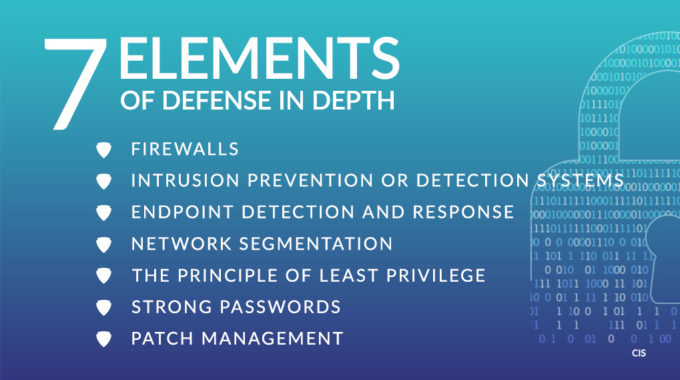
To keep sophisticated cyberthreats at bay, you need a robust DiD strategy. Your strategy should involve layering multiple defensive methods, like firewalls, intrusion prevention and detection systems, endpoint detection and response (EDR), network segmentation, etc., to build a security fortress that’s hard to crack.
DiD is an undertaking that takes time and effort, so it’s best to collaborate with a partner like us who can implement and maintain your DiD strategy while you focus on your business.
If you want to learn more about how DiD can help protect your business, download our free eBook “7 Elements of an Effective Defense in Depth (DiD) Security Strategy” below.
Download Your Free eBook!
Source:
- Statista
About Speors, Inc
Speros is a technology provider in Savannah, GA. We provide multiple business services including, IT support, managed services, Telephony Services, Surveillance Installation and Maintenance, Web and Graphic Design Services, Audiovisual Solutions, and more. Speak to a representative today to learn more about our business services.